Most enterprise buyers now ask for proof of security before they sign a contract. They don’t just want a nice pitch deck or a list of products; they want to see real evidence that you operate securely. A SOC 2 gap assessment shows whether your existing practices meet the American Institute of Certified Public Accountants (AICPA) Trust Services Criteria (TSC) and helps your team find deficiencies before an external auditor does. This SOC 2 Gap Assessment Guide explains what a gap assessment is, why it matters for growing companies, and how to run one effectively. Readers will gain a practical understanding of gap analysis, the difference between a gap assessment and a full audit, and how this process supports audit readiness and stronger security controls.
What Is a SOC 2 Gap Assessment?
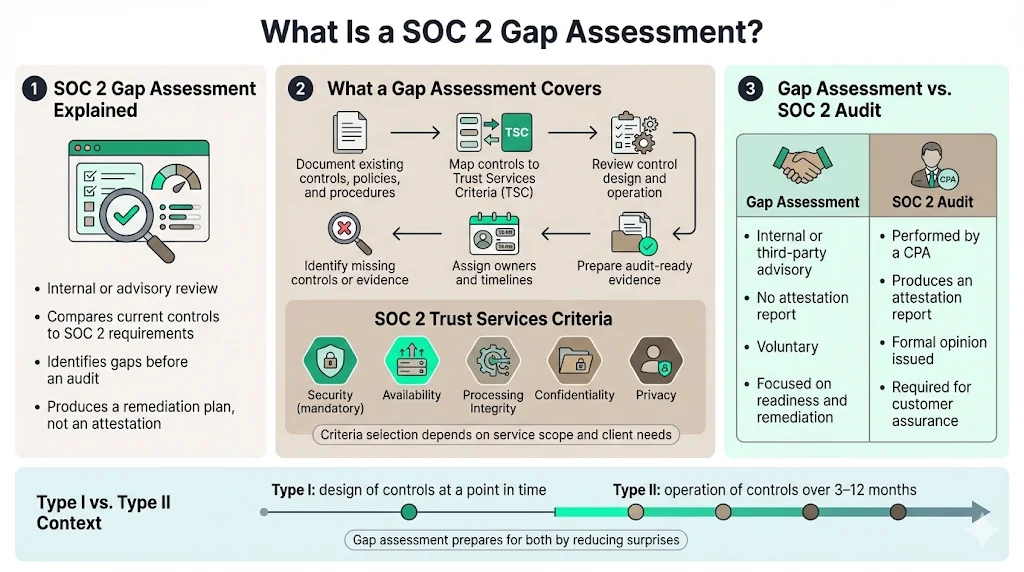
A gap assessment compares your current controls, policies, and evidence to the SOC 2 requirements. It is not the same as a full compliance audit. An audit produces an attestation report and is performed by an independent certified public accountant, while a gap analysis is an internal review to see where you stand. Thoropass describes a SOC 2 gap analysis as a systematic process that identifies the differences between an organization’s security and compliance practices and the requirements of the SOC 2 Trust Services Criteria. It helps teams identify control deficiencies and create a remediation plan before starting an audit.
The Trust Services Criteria cover five categories: Security, Availability, Processing Integrity, Confidentiality, and Privacy. The security category is mandatory for all SOC 2 reports, while the other criteria may be selected based on the nature of your service and client needs. A gap assessment typically includes the following:
-
Documenting your current controls, policies, and procedures.
-
Mapping those controls to the relevant TSC categories.
-
Testing control design and operational effectiveness.
-
Identifying missing controls or documentation.
-
Creating a remediation plan with owners and timelines.
-
Preparing evidence that supports eventual audit fieldwork.
Unlike a SOC 2 Type I or Type II audit, a gap assessment does not result in an attestation report. It is voluntary and can be performed by an internal team or a third party. In a Type I audit the auditor tests whether your controls are designed suitably at a point in time. A Type II audit covers how controls operate over a period of three to twelve months and involves more detailed evidence. A gap assessment, therefore, is a preparation stage that helps you avoid surprises in either type of audit.
Gap assessment vs. full compliance audit
A certified public accountant performs a full SOC 2 audit following AICPA standards. It produces an attestation report that can be shared with customers. The audit includes control testing by the auditor and a formal opinion on whether your controls meet the TSC. A gap assessment, by contrast, is an internal or advisory review that looks at your controls from the auditor’s perspective and identifies deficiencies. The goal is to develop a remediation plan before starting the audit. This reduces the risk of failing control tests and accelerates the audit timeline. Gap analysis covers the scope of your system, existing documentation, and preliminary control testing, but it stops short of issuing an opinion.
Why Gap Assessment Matters for Enterprise‑Focused Teams
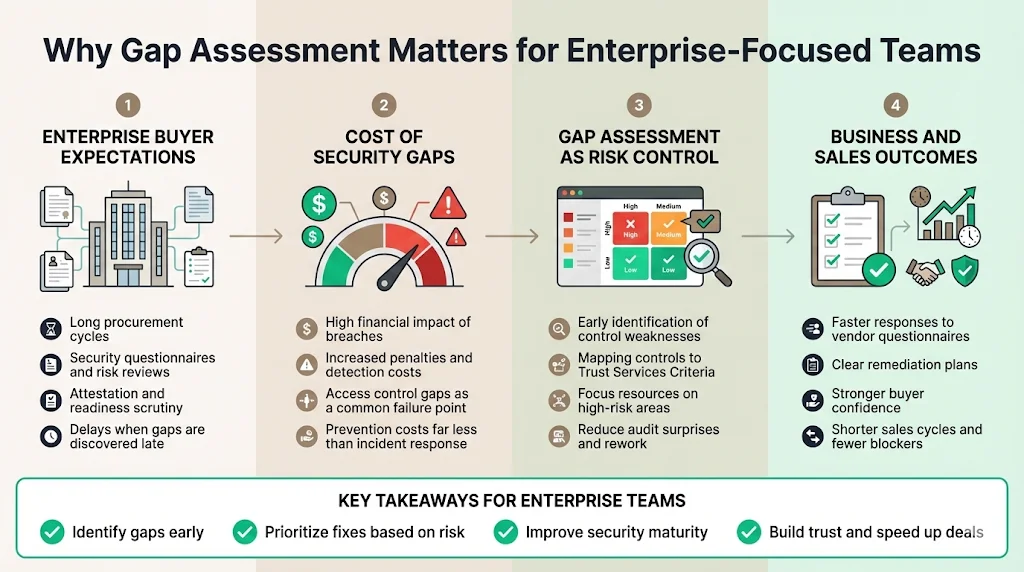
Selling to enterprises often involves long procurement cycles and strict security due diligence. Customers will ask for security questionnaires, vendor risk assessments, and third‑party attestation reports. A gap assessment helps reduce the risk of delays and negative findings during these processes. Thoropass explains that a gap analysis provides strategic business value by revealing where controls are weak, enabling resource optimization and risk mitigation. Cherry Bekaert notes that the readiness phase where companies map controls to the TSC and identify gaps can take one to two months, so starting early helps teams avoid last‑minute rushes.
From the buyer’s perspective, a solid gap assessment can shorten sales cycles. Buyers need assurance that vendors handle data securely, particularly when handling regulated data such as health information or personal data. IBM’s 2025 Cost of a Data Breach report shows that the global average cost of a breach dropped slightly to USD 4.44 million, but the United States average exceeded USD 10 million due to steep penalties and detection costs. The report also found that 97% of breaches involving artificial intelligence systems lacked proper access controls. These numbers show how expensive security failures can be. By conducting a gap assessment, you can find access control gaps and fix them before an incident occurs, reducing potential costs and building trust with buyers.
Gap assessments also support internal risk management. According to the NIST Risk Management Framework, risk assessment involves identifying threat sources, vulnerabilities, impacts, and likelihood, and then prioritizing risks. Doing this early allows teams to focus resources where they matter most. The readiness phase of a SOC 2 program is an opportunity to document controls, perform initial tests, and develop mitigation plans. With a proper gap assessment, you can flag missing documentation, undefined internal controls, or confusion around risk management before they block your audit or procurement processes.
Main takeaways for enterprise‑focused teams include:
-
Early identification of compliance gaps: A gap assessment finds control deficiencies before they become audit findings.
-
Efficient resource allocation: By prioritizing gaps based on risk, teams can focus on high‑impact controls rather than trying to fix everything at once.
-
Stronger security posture: Addressing gaps improves your program’s maturity and reduces the likelihood of breaches.
-
Shorter sales cycles and improved trust: With a clear remediation plan and evidence of controls, you can answer vendor questionnaires quickly and satisfy enterprise buyers.
Core Components of a SOC 2 Gap Assessment
An effective gap assessment follows a structured process. The steps described below provide a framework for examining your controls and developing a remediation plan.
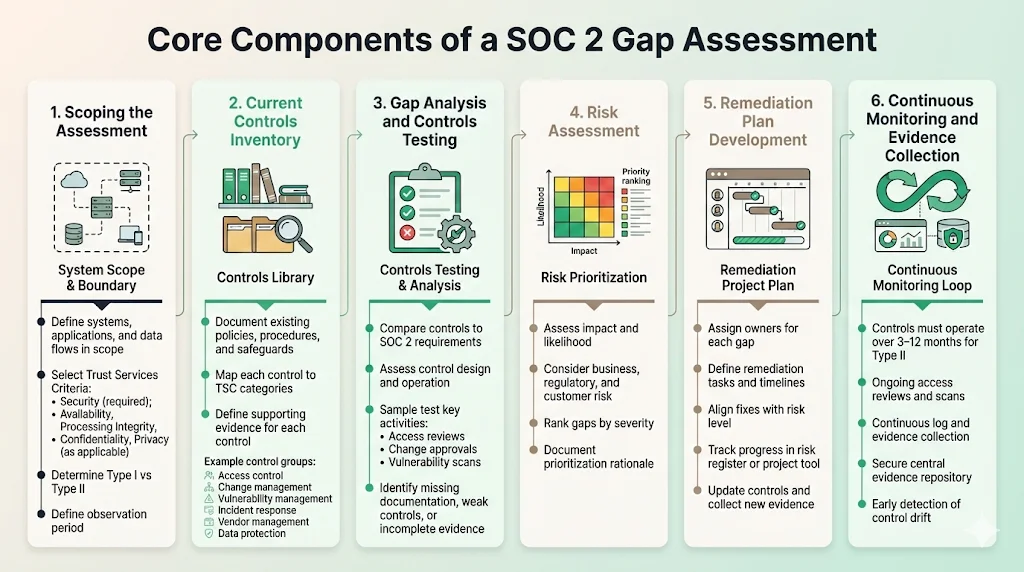
1) Scoping the Assessment
The first step is to define the boundaries of your system. Identify which systems, applications, and data flows are in scope for the SOC 2 report. Define which TSC categories apply to your service. The security criterion is required, and others such as availability, processing integrity, confidentiality, and privacy are optional. If you handle personal data or promise high uptime, you may include additional criteria to satisfy customer requirements. Scoping also involves determining the type of report (Type I or Type II) and the observation period.
2) Current Controls Inventory
Next, document your current controls. This includes policies, procedures, technical safeguards, and physical safeguards. A control inventory should map each control to a TSC category and describe the evidence that supports its design and operation. Examples of controls include:
-
Access control: Policies for granting and reviewing user access, multi‑factor authentication, and least‑privilege principles.
-
Change management: Procedures for code deployment, approvals, and rollback.
-
Vulnerability management: Processes for scanning, triaging, and remediating vulnerabilities; service agreements (SLAs) based on the Common Vulnerability Scoring System (CVSS).
-
Incident response: Plans for detecting, responding to, and reporting security incidents.
-
Vendor management: Due diligence on third‑party vendors; contracts with security obligations; review of service organization reports.
-
Data protection: Encryption of data in transit and at rest; logging and monitoring; backup and recovery.
For each control, gather evidence such as policy documents, system configurations, logs, and reports. This evidence will be required during the audit, so collecting it during the gap assessment saves time later.
3) Gap Analysis and Controls Testing
Gap analysis involves comparing your documented controls to the SOC 2 requirements. Ask whether each control meets the design requirements of the relevant TSC and whether it operates effectively. For example, if you claim to perform quarterly access reviews, can you show evidence of those reviews? Do you have change‑management tickets with approvals? Are vulnerability scans run regularly and tracked to closure? Conduct sample testing to verify these practices. Thoropass explains that gap analysis evaluates data processed, where data resides, how data flows, and who has access. It also identifies whether controls cover each dimension adequately.
During this stage, identify areas where documentation is missing, controls are poorly designed, or evidence is incomplete. Create a list of deficiencies with context. For each deficiency, record the TSC criterion, the current state, and the desired state. This will inform the remediation plan.
4) Risk Assessment
Once gaps are identified, assess their risk impact and likelihood. NIST’s guidance emphasises identifying threat sources, vulnerabilities, impacts, and likelihood, and then prioritising risks. The assessment should consider business impact, customer commitments, regulatory requirements, and likelihood of exploitation. Use a risk matrix or scoring method to rank gaps. For example, a missing access control review for systems containing personal data is high risk and should be fixed immediately, whereas a missing procedure for lower‑impact systems may be medium risk. Document the rationale for risk prioritization and use it to plan remediation.
5) Remediation Plan Development
Turn the findings into a remediation plan. For each gap, assign an owner, define the tasks needed to fix it, and set timelines. Ensure that remediation tasks match risk rankings and enterprise requirements. For instance, if you identify that backup procedures are not tested, the remediation plan might involve updating backup scripts, scheduling periodic recovery drills, and documenting the results. Track progress in a project management tool or risk register. The plan should include resource estimates and dependencies. During remediation, update policies, implement new controls, and gather evidence that shows the control operates effectively.
A real gap assessment finds security weaknesses, not just missing documents.
Drop your work email and find the control deficiencies before your auditor does.
6) Continuous Monitoring and Evidence Collection
After remediation, maintain your controls and continue collecting evidence. SOC 2 Type II audits require evidence that controls operated effectively over an observation period of three to twelve months. Continuous monitoring helps ensure that controls do not drift over time. For example, run periodic access reviews, vulnerability scans, and audit log reviews. Collect and store evidence in a secure repository so it is ready for auditors. Documenting controls early and continuously reduces the time needed during audit fieldwork. Continuous monitoring also enables you to detect and respond to incidents quickly, preventing breaches and fines.
SOC 2 Gap Assessment Checklist
To make the assessment actionable, use a checklist. The checklist below summarises the steps and ensures that you cover all essential tasks. Adjust it based on your organisation’s scope and TSC.
-
**Define scope and criteria:
**
-
Identify systems, services, and data flows in scope.
-
Select the TSC categories (security is required; availability, processing integrity, confidentiality, privacy as needed).
-
Determine Type I or Type II and observation period.
-
-
**Document existing internal controls:
**
-
Inventory policies, procedures, technical controls, and physical controls.
-
Map controls to TSC categories.
-
Gather initial evidence (documents, logs, configurations).
-
-
**Perform controls testing:
**
-
Evaluate control design and operating effectiveness.
-
Sample evidence for access controls, change management, vulnerability management, incident response, vendor management, and data protection.
-
-
**Identify control deficiencies:
**
-
Compare existing controls to SOC 2 requirements.
-
Record missing controls, weak control design, or lack of evidence.
-
Record the TSC category and affected systems.
-
-
**Map gaps to requirements and assess risk:
**
-
Determine the impact and likelihood of each gap.
-
Prioritise gaps based on risk and business impact.
-
Use a risk matrix or scoring method.
-
-
**Build remediation plans:
**
-
Assign owners to each gap.
-
Define tasks, resources, and deadlines.
-
Make sure tasks correspond with risk priorities and enterprise buyer requirements.
-
-
**Assign responsibilities and track progress:
**
-
Use a project management tool or risk register.
-
Monitor remediation progress and adjust plans as needed.
-
Escalate issues that threaten audit readiness.
-
-
**Implement continuous monitoring:
**
-
Schedule periodic control testing (access reviews, vulnerability scans, log reviews).
-
Collect and store evidence regularly.
-
Prepare for audit by keeping documentation up to date.
-
This assessment checklist uses the keywords “audit readiness,” “internal controls,” “security posture,” “controls testing,” and “assessment checklist” to reinforce the process.
Common Challenges and How to Solve Them
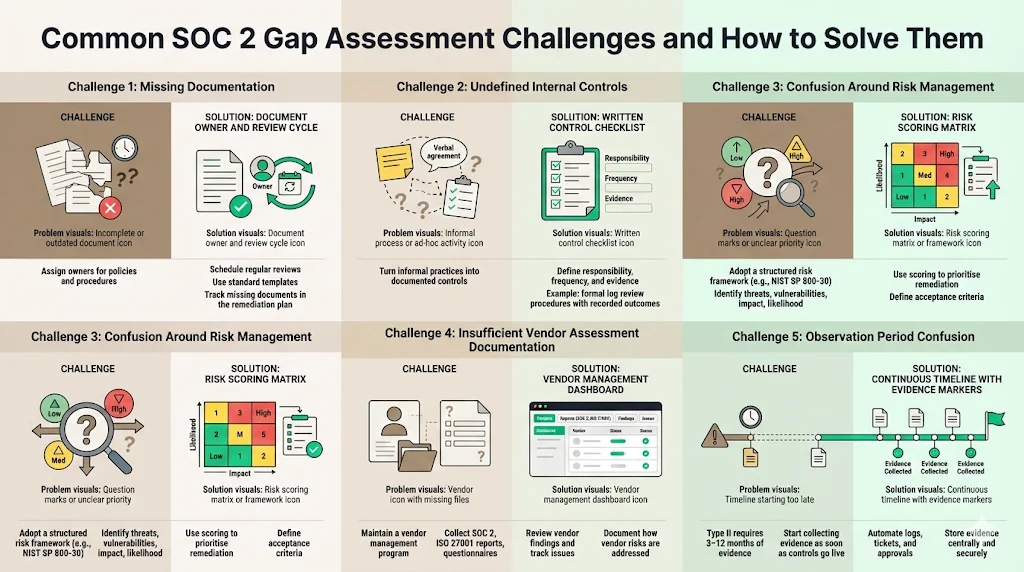
Teams often encounter obstacles during a gap assessment. The following issues and solutions can help you avoid common pitfalls.
-
Missing documentation: Policies or procedures may not be documented or are outdated. Solution: assign documentation owners and establish a regular review cycle. Use templates for policy documents to ensure consistency. During gap analysis, identify missing documents and include them in the remediation plan.
-
Undefined internal controls: Some security activities happen informally without defined controls. Solution: formalise these activities as written controls with clear responsibilities, frequency, and evidence. For example, if engineers check logs when incidents occur but there is no documented log review process, create a procedure that specifies who reviews logs, when, and how findings are recorded.
-
Confusion around risk management: Teams may not know how to prioritise gaps or decide what “good enough” looks like. Solution: adopt a risk management framework such as NIST SP 800‑30, which provides guidance on identifying threats, vulnerabilities, impacts, and likelihood. Use risk scoring to prioritise remediation and provide clear criteria for acceptance.
-
Insufficient vendor assessment documentation: Many organisations rely on cloud services and third‑party vendors. If due diligence documents are missing or incomplete, this can create gaps. Solution: maintain a vendor management program. Collect service organisation reports (SOC 2, ISO 27001), security questionnaires, and contractual commitments. Establish a process to review vendor reports, track issues, and document how vendor risks are managed.
-
Observation period confusion: For Type II reports, teams may not understand that auditors will look for evidence covering three to twelve months. Starting monitoring too late can cause delays. Solution: start evidence collection as soon as controls are implemented. Use automation tools to capture logs, tickets, and approvals, and store them in a secure repository.
Tools and Resources for Faster SOC 2 Gap Assessment
Several tools can help map controls to the SOC 2 TSC and track gaps. Governance, risk, and compliance (GRC) platforms can centralise controls, evidence, and remediation tasks. They often provide control libraries, questionnaires, and workflow automation. However, tools alone are not enough. Your team still needs expertise to interpret requirements, test controls, and make risk‑based decisions.
Working with a managed security and compliance provider can accelerate readiness. For example, Konfirmity is a human‑led, managed service that has supported more than 6,000 audits and brings over 25 years of combined technical expertise. Instead of requiring your team to spend hundreds of hours on self-serve GRC software, a managed service implements controls inside your stack, monitors them year‑round, and guides you through the audit process. Such services often offer dedicated experts, continuous monitoring, evidence collection, and remediation tracking, enabling your team to focus on building products while staying audit‑ready.
Bridging Gap Assessment to SOC 2 Audit Success
A thorough gap assessment directly supports a smoother SOC 2 audit. It feeds into audit readiness by ensuring that controls are documented, tested, and remediated before the auditor arrives. By fixing deficiencies early, you reduce the chance of surprise findings during the audit and avoid delays in report delivery.
SOC 2 Type I and Type II audits require different levels of evidence. Cherry Bekaert notes that Type I fieldwork can take weeks to one or two months, while Type II fieldwork covers an observation period of three to twelve months and can take up to two months of fieldwork. BEMO describes that self‑managed SOC 2 programs can take six to eighteen months, including pre‑audit preparation (one to three months), observation (three to twelve months), audit (one to three weeks), and report delivery (two to six weeks). With expert guidance, readiness can be achieved faster. At Konfirmity, typical SOC 2 readiness takes four to five months instead of nine to twelve months when self‑managed, and it reduces internal effort from roughly 550–600 hours to about 75 hours per year. While internal numbers vary, the principle is that a guided approach saves time and resources.
A strong gap assessment improves dialogue with external auditors. When auditors see a well‑documented control matrix, risk assessments, and remediation evidence, they can focus their testing on high‑risk areas. This leads to fewer information requests and a more collaborative audit. Early gap findings also save stress: if you find that change‑management documentation is missing, you can fix it before the observation period begins rather than scrambling during the audit.
Additional Considerations for Enterprise‑Selling Companies
Enterprise buyers often send security questionnaires, data processing agreements (DPAs), and business associate agreements (BAAs). A gap assessment helps you respond confidently. Adjust your messaging for enterprise security buyers by addressing how you meet TSC categories, handle personal data, and enforce internal controls. Document how your controls map to frameworks like ISO 27001, HIPAA, and GDPR. This cross‑framework mapping allows you to reuse evidence across multiple obligations. For example, many controls used in SOC 2 (such as access management, incident response, and vendor risk management) also satisfy ISO 27001 Annex controls and HIPAA safeguards.
When preparing for enterprise procurement, create enterprise‑ready documentation:
-
Security questionnaires: Provide evidence of controls (policies, procedures, audit reports).
-
DPAs and BAAs: Document data handling practices, encryption, breach notification procedures, and sub‑processor oversight.
-
Policies and procedures: Prepare drafts of your information security policies, incident response plan, and change‑management procedures.
-
Artifacts: Have copies of your latest SOC 2 report, penetration test results, vulnerability scans, and certifications.
These materials reduce back‑and‑forth with procurement teams and shorten the contracting cycle. If you operate in healthcare, keep in mind that HIPAA violations carry steep fines: Tier 1 penalties range from $137 to $63,973 per violation, and Tier 4 violations start at $63,973 per violation with annual caps of $2 million. These penalties illustrate why enterprise buyers require assurance that vendors comply with security and privacy obligations.
Conclusion
This SOC 2 Gap Assessment Guide emphasises that a SOC 2 gap assessment is not just a box to check; it is a practical tool for building a real security program.
A SOC 2 gap assessment is not just a box to check; it is a practical tool for building a real security program that stands up to enterprise buyers and auditors. It reveals where your controls fall short, prioritises remediation based on risk, and prepares you for a smoother audit. For companies selling to enterprise clients, a gap assessment reduces procurement friction, shortens sales cycles, and builds trust. It also strengthens your security posture, making incidents less likely and reducing the cost of breaches. When combined with a human‑led, managed service like Konfirmity, the process becomes an outcome‑as‑a‑service model: dedicated experts implement controls inside your stack, monitor them year‑round, and guide you to audit readiness. Rather than chasing compliance checkboxes, start with security, operate it daily, and let compliance follow.
FAQs
1) What is ISO 27001 compliance for data security?
ISO 27001 is an international standard for establishing, implementing, maintaining, and improving an information security management system (ISMS). It sets requirements for building an ISMS so organisations can systematically protect sensitive data. Certification demonstrates that your ISMS meets the standard’s requirements and supports continuous improvement.
2) Does ISO 27001 require data‑loss prevention (DLP)?
The standard does not prescribe specific tools. ISO 27001 expects organisations to implement appropriate controls based on their risk assessment. This may include controls for preventing data loss, but the choice of technology (such as DLP software) depends on the context and risks. During the risk assessment phase, organisations identify where sensitive data resides and decide which controls are needed to protect it.
3) What are ISO 27017 and ISO 27018?
ISO 27017 and ISO 27018 are cloud‑focused extensions of ISO 27001. ISO 27017 provides guidance on implementing cloud‑specific security controls for both cloud providers and customers. It clarifies shared responsibilities and introduces new controls for cloud environments. ISO 27018 focuses on protecting personally identifiable information in public clouds and extends ISO 27002 controls to include privacy protections. These extensions are assessed as part of an ISO 27001 audit but offer additional guidance for cloud services.
4) What is the name for ISO 27001 in data security?
ISO 27001 is commonly referred to as the international standard for information security management systems. It doesn’t have another name; the number 27001 identifies the standard and distinguishes it from related standards such as ISO 27017 (cloud security) and ISO 27018 (cloud privacy). Organisations refer to it simply as “ISO 27001 certification” when discussing their adherence to the standard.