Most large customers now ask for evidence that vendors operate real security controls before they sign a contract. Procurement teams expect to see detailed audit reports and certification letters. Without day‑to‑day security and continuous evidence, deals stall — even when a team thinks its program looks good on paper.
In this guide I explain ISO 27001 Mapping To SOC 2 — what it means, why enterprise sellers care, and how to do it. I draw on more than twenty‑five years of security and compliance work at Konfirmity, where we’ve helped companies through more than six thousand audits. The aim is to show how mapping these frameworks cuts duplication, speeds due diligence, and delivers controls that stand up to auditors and buyers.
Background: ISO 27001 and SOC 2 fundamentals
ISO 27001 — an international blueprint for managing risk
ISO/IEC 27001 is the world’s best‑known standard for building an information‑security management system (ISMS). It defines requirements for establishing, implementing, maintaining and continually improving an ISMS. In simple terms, it gives organisations a structured way to identify risks, implement controls, and keep improving. A few important points:
-
Risk‑driven management system. ISO 27001 promotes a holistic approach that covers people, policies and technology. It forces you to document the scope of your ISMS, conduct risk assessments, and select appropriate controls.
-
Clauses and Annex A controls. The standard contains ten main clauses and an Annex A with 93 controls. These controls were updated in 2022 — grouped into organisational, people, physical and technological categories and modernised to address issues like threat intelligence, data masking and cloud services.
-
Certification cycle. Unlike SOC 2, ISO 27001 requires a formal certification. The 2022 version must be adopted by 31 October 2025. Certificates are valid for three years, with annual surveillance audits and a full recertification at the end of the cycle.
SOC 2 — a U.S. attestation focused on operating controls
SOC 2 is part of the AICPA’s System and Organization Controls suite. It isn’t a certification but an auditor’s opinion on whether controls at a service organisation are suitably designed and operating effectively. The report addresses control objectives relevant to security, availability, processing integrity, confidentiality and privacy. Key features include:
-
Trust Services Criteria (TSC). SOC 2 reports are built around five categories: security, availability, processing integrity, confidentiality and privacy. The security category (common criteria) is mandatory; the others are optional depending on the service commitments.
-
Type I vs. Type II. Type I evaluates design at a point in time; Type II assesses operating effectiveness over a period (often three to twelve months). Evidence must show that controls, such as access reviews and change‑management approvals, operated throughout the observation window.
-
Attestation vs. certification. A SOC 2 report is an attestation prepared by a licensed CPA firm; there is no “SOC 2 certificate.” Reports are renewed annually.
Why businesses seek both
Enterprise clients often ask for both ISO 27001 certification and SOC 2 because they serve different markets and provide different assurance types. ISO 27001 is globally recognised and proves that a structured ISMS exists, while SOC 2 is widely requested by U.S. buyers and focuses on how controls operate. A mapping spreadsheet published by the AICPA shows that about 80% of ISO 27001 and SOC 2 control requirements overlap. Additionally, secureframe’s 2026 statistics report notes that 81% of organisations had a current or planned ISO 27001 certification in 2025, up from 67% in 2024, signalling growing demand for dual compliance.
Core similarities and differences
Shared goals and philosophy
Both ISO 27001 and SOC 2 aim to protect sensitive data and reassure customers. They emphasise:
-
Risk assessment and continuous improvement. ISO 27001 mandates periodic risk assessments and corrective actions, while SOC 2’s common criteria require risk assessment and monitoring (CC3 and CC4).
-
Information‑security governance. Both frameworks expect policies, management commitment, and oversight. ISO 27001 has clauses on leadership and support; SOC 2’s CC1 and CC2 focus on control environment and communication.
-
Vendor oversight and supply chain security. ISO 27001 includes supplier security controls, and SOC 2 points of focus encourage vendor risk management.
-
Monitoring and incident response. Both require logging, monitoring and response procedures. SOC 2 CC6 to CC8 cover access controls, system operations and change management. ISO 27001 includes controls for logging, incident management and business continuity (Annex A sections 8.15–8.35).
Key differences you must know
Understanding the differences helps decide whether you need one or both frameworks and informs the mapping process:
Aspect
ISO 27001
SOC 2
Scope
Focuses on establishing and operating an ISMS; defines organisation-wide policies, procedures and risk management.
Assesses the design and operating effectiveness of controls relevant to specific trust services criteria.
Structure
Ten clauses plus Annex A with 93 prescribed controls (reduced and grouped in 2022).
A set of high-level Trust Services Criteria with nine common criteria and additional criteria for availability, processing integrity, confidentiality and privacy.
Flexibility
All controls apply unless justified in a Statement of Applicability; limited flexibility.
Organisations choose which criteria to include; typical SOC 2 requires between 70 and 150 controls depending on scope.
Deliverable
Certification issued by an accredited registrar; valid for three years, with surveillance audits.
CPA attestation report; no certificate; renewed annually.
Geography & use cases
Widely recognised worldwide; often requested by international customers and regulators.
U.S. buyers and cloud services prefer SOC 2; some clients accept ISO 27001 but still expect a SOC 2 report.
Audit timeline and cost
Average 4 months to get audit-ready; stage 1 and stage 2 audits take about 6 months; certification can cost USD 10–50K.
Type I readiness averages 3 months; Type II readiness 4 months; the audit period can last 3–12 months; costs range from USD 10–60K.
These distinctions mean SOC 2 cannot replace ISO 27001 and vice versa. They address different audiences and deliver different forms of assurance.
Why mapping matters for enterprise sellers
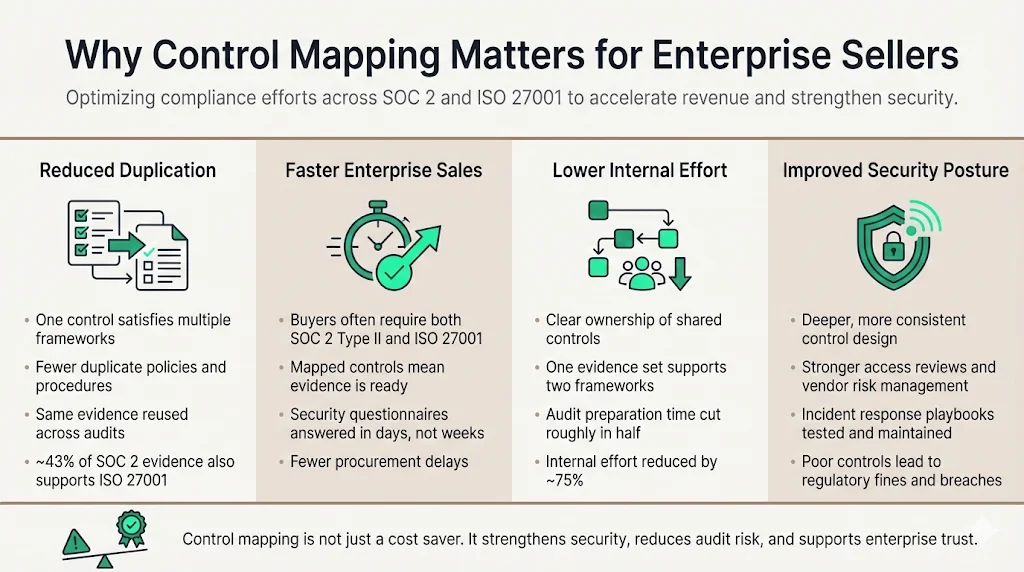
Dual compliance is expensive if approached separately. Mapping solves that problem. In our experience:
-
Reduced duplication. By identifying controls that satisfy both frameworks, teams avoid writing multiple policies or collecting the same evidence twice. A‐LIGN’s 2025 benchmark report found that roughly 43% of SOC 2 evidence also satisfies ISO 27001 requirements.
-
Faster sales cycles. Buyers often ask for a current SOC 2 Type II report and an ISO 27001 certificate. Vendors who maintain continuous evidence and map controls up front typically answer security questionnaires in days rather than weeks.
-
Smaller team burden. With a unified program, control owners know which evidence supports both frameworks. In practice, mapping has cut audit preparation time by half and reduced internal effort by about 75%.
-
Improved resilience. Mapping encourages deeper control design. Teams implement robust access reviews, vendor risk management and incident‑response playbooks that stand up to auditors and attackers. Fine amounts show why this matters: in 2025 the UK Information Commissioner’s Office levied fines of £14 million, £3.07 million, £2.31 million and £1.23 million on organisations following cyber‑attacks. These penalties emphasise the cost of poor security controls.
How mapping works step by step
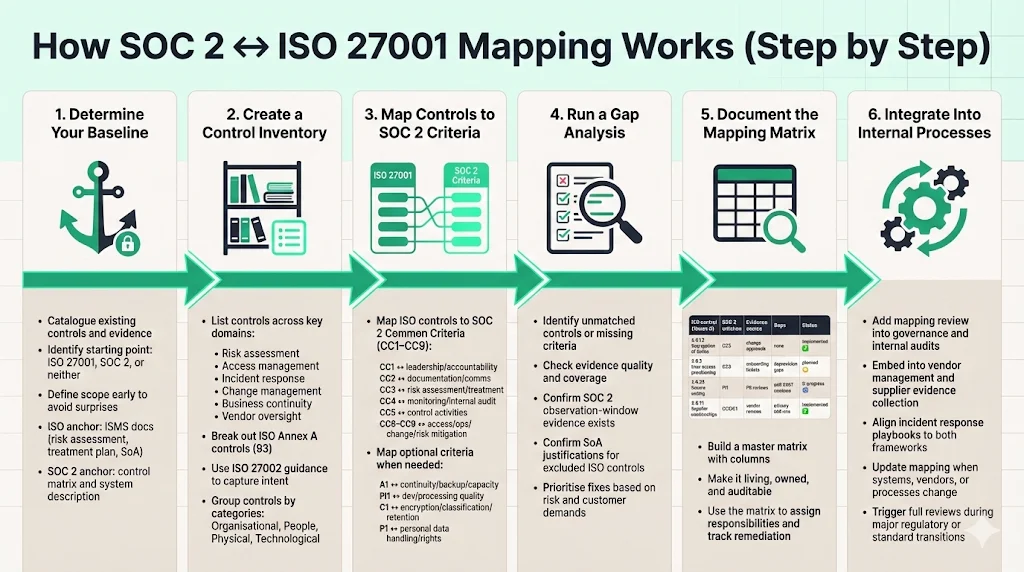
Determine your baseline
Begin by cataloguing your existing controls. Gather policies, procedures, risk assessments, technical configurations, and evidence logs. Identify whether you already operate under ISO 27001, SOC 2, or neither. Defining the scope early prevents surprises later. If you are starting from ISO 27001, your ISMS documentation (risk assessment, treatment plan, Statement of Applicability) becomes the baseline. If you start with SOC 2, your control matrix and system description serve as the anchor.
Create a control inventory
List controls across risk domains: risk assessment, access management, incident response, change management, business continuity and vendor oversight. Break down ISO 27001 Annex A into its 93 controls. Use ISO 27002 guidance to capture the intent and attributes of each control. For example, the 2022 edition grouped controls into organisational, people, physical and technological categories and introduced new controls for threat intelligence, data masking, secure coding and cloud services. A thorough inventory helps map each control to the corresponding SOC 2 criteria.
Map controls to Trust Services Criteria
Next, match each ISO 27001 control to the relevant SOC 2 criterion. Start with the common criteria (CC1–CC9):
-
CC1: Control environment ↔ ISO 27001 clauses on leadership, support and accountability.
-
CC2: Information and communication ↔ ISO controls on documentation, training and reporting.
-
CC3: Risk assessment ↔ ISO risk assessment and treatment planning.
-
CC4: Monitoring activities ↔ ISO internal audit and management review requirements.
-
CC5: Control activities ↔ ISO Annex A controls (e.g., access control, cryptography).
-
CC6–CC9: Logical/physical access, system operations, change management, risk mitigation ↔ ISO Annex A controls on access control, system maintenance, secure development and supplier security.
For optional SOC 2 criteria, map accordingly:
-
Availability (A1) ↔ ISO controls on capacity management, backup, disaster recovery and business continuity.
-
Processing integrity (PI1) ↔ ISO controls on development, validation and data processing quality.
-
Confidentiality (C1) ↔ ISO controls on encryption, classification and retention.
-
Privacy (P1) ↔ ISO controls on personal data handling, consent and data subject rights; augment with GDPR or HIPAA requirements if applicable.
Document where evidence needs to change. For example, ISO 27001 requires a documented risk treatment plan, while SOC 2 may only need evidence that risks are assessed and mitigated. SOC 2 also emphasises the observation window, so ensure that controls produce ongoing logs and approvals.
Run a gap analysis
Compare your mapped controls against both frameworks to identify gaps. Questions to ask:
-
Are there ISO 27001 controls without a corresponding SOC 2 criterion?
-
Are there SOC 2 criteria (e.g., privacy) that you’ve not addressed through ISO 27001 controls?
-
Does your evidence cover the SOC 2 observation window?
-
Do you have documented justification for excluded ISO controls (Statement of Applicability)?
Prioritise missing controls based on risk and client requirements. For example, if a major customer requires the privacy criterion, address gaps in data‑subject rights and breach notification processes. Address high‑risk gaps promptly and plan remediation tasks.
Mapping ISO 27001 to SOC 2 works best when real controls underpin both frameworks.
Drop your work email and we'll build a unified control set that satisfies both audits.
Document control mapping
Create a mapping matrix that shows the relationship between ISO controls and SOC 2 criteria, the evidence source, any gaps, and current status. This becomes your master reference for audits. An example of a simple mapping matrix is shown below.
ISO 27001 control (Annex A)
SOC 2 criterion
Evidence source
Gaps
Status
A 6.1.2 – Segregation of duties
CC5 – Control activities
Access control policy; change-approval logs
None
Implemented
A 8.3 – User access provisioning
CC6 – Logical access controls
HR onboarding checklist; access request tickets
Evidence of deprovisioning not captured across all apps
Planned improvement
A 8.28 – Secure coding
PI1 – Processing integrity
Pull-request templates; code-review records
Controls mapped but need periodic static code analysis
In progress
A 8.31 – Supplier relationships
CC5 / C1 – Control activities / Confidentiality
Vendor risk assessments; signed DPA/BAA
Mapping to privacy criterion may require additional DPAs
Implemented
A living matrix makes it easier to assign responsibilities, track remediation and provide auditors with a clear cross‑reference.
Integrate into internal processes
Mapping isn’t a one‑time project. To make it effective:
-
Incorporate into governance. Add mapping reviews to management meetings and internal audits. Use the matrix to track control ownership and evidence production.
-
Embed in vendor management. Collect evidence from suppliers that meet both ISO and SOC 2 criteria. Require vendors to provide their own SOC 2 reports or certifications as part of due diligence.
-
Build into incident handling. Incident‑response playbooks should satisfy SOC 2 (CC7) and ISO controls on event management and communications. After each incident, update risk assessments and mapping.
-
Schedule periodic updates. Review the mapping whenever you add new systems, adopt cloud services, or change business processes. Regulatory changes (such as the ISO 27001:2022 transition deadline) are good triggers for a full review.
Templates and tools
Control mapping matrix template
A simple spreadsheet or GRC platform can capture mappings. At minimum include these columns: ISO control reference, SOC 2 criterion, evidence source (policy or log), gap description, status, owner and review date. Populate it regularly and use it to demonstrate coverage to auditors and clients.
Risk assessment log template
Use a table or tool to document threats, existing controls and how each control aligns with ISO 27001 and SOC 2:
Threat
Impact
Existing controls
Framework alignment
Action
Credential stuffing
Account takeover; service outage
Multi-factor authentication (A 8.3), login throttling, monitoring alerts
ISO: access control; SOC 2: CC6 (logical access), CC7 (system operations)
Review MFA coverage and alert tuning
Third-party breach
Exposure of personal data
Vendor risk assessment (A 5.19), signed data processing agreements, periodic assessments
ISO: supplier relationships; SOC 2: CC5 (control activities), C1 (confidentiality)
Update risk register; request vendors’ SOC 2 reports
Insider misuse
Theft of client data
Role-based access control, logging, separation of duties
ISO: A 8.2 (privilege management), A 8.4 (user registration), A 8.15 (logging); SOC 2: CC6, CC7
Increase frequency of access reviews; monitor high-privilege accounts
Audit readiness checklist
Prepare ahead of your external audit or attestation with a checklist such as:
Item
Evidence
Responsible person
Status
Risk assessment completed and documented
Risk register, treatment plan
CISO
Done
Policies approved and communicated
Information security policy; code of conduct
HR & Legal
Done
Access reviews conducted quarterly
Access review logs; remediation tickets
IT Operations
In progress
Vendor assessments performed
Vendor due-diligence reports; BAA/DPA
Procurement
Pending
Incident response testing completed
Tabletop exercise report; lessons learned
Security team
Scheduled
Recommended tools and automation
Mapping and evidence collection can be done manually, but automation reduces errors and saves time. Platforms like Secureframe, Vanta or A‑LIGN centralise control documentation, collect evidence from sources such as GitHub or AWS, and generate mapping matrices. According to Konfirmity’s delivery experience, automation combined with human oversight can cut audit preparation time in half and free hundreds of hours otherwise spent chasing screenshots or log extracts. The right tooling also enforces observation windows for SOC 2 Type II, schedules recurring tasks (access reviews, vendor risk assessments) and maintains version control of policies.
Common challenges and how to avoid them
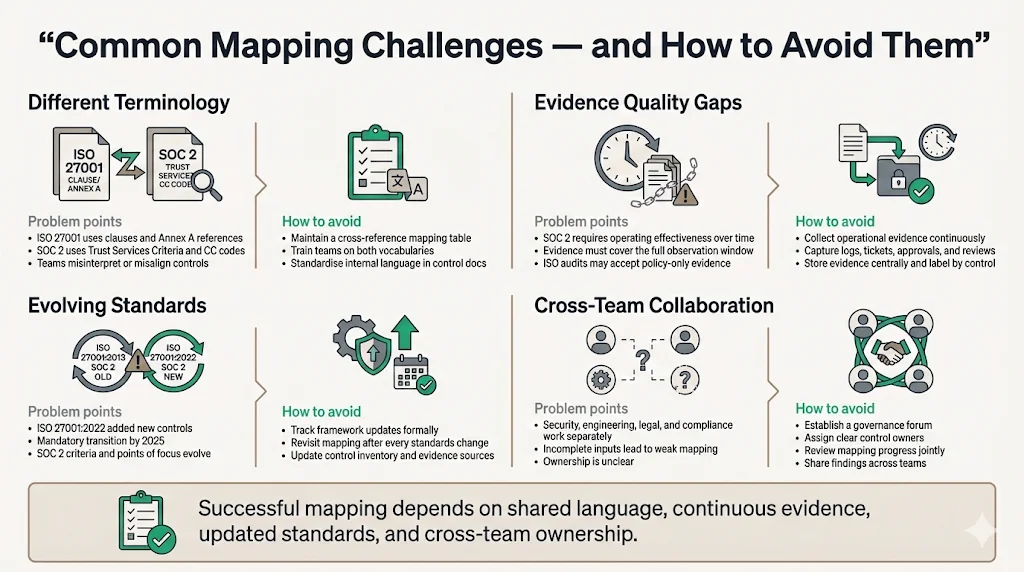
-
Different terminology. ISO 27001 uses specific clause numbers and Annex A references; SOC 2 uses criteria names and common criteria codes. Teams sometimes mis-interpret the mapping. Use a cross‑reference table and train staff on both vocabularies.
-
Evidence quality. SOC 2 audits focus on operating effectiveness over time. Evidence such as access logs, change‑management tickets and incident reports must cover the observation period. ISO 27001 auditors may accept policy statements alone. To avoid gaps, collect operational evidence continuously and store it centrally.
-
Evolving standards. ISO 27001:2022 introduced new controls and requires transition by 2025. SOC 2 criteria are periodically updated (e.g., revised points of focus in 2022). Review your mapping whenever standards change and update your control inventory.
-
Collaboration across teams. Security, engineering, legal and compliance teams often work in silos. Mapping requires input from all. Establish a governance forum where control owners review mapping progress and share insights.
Best practices for ongoing compliance
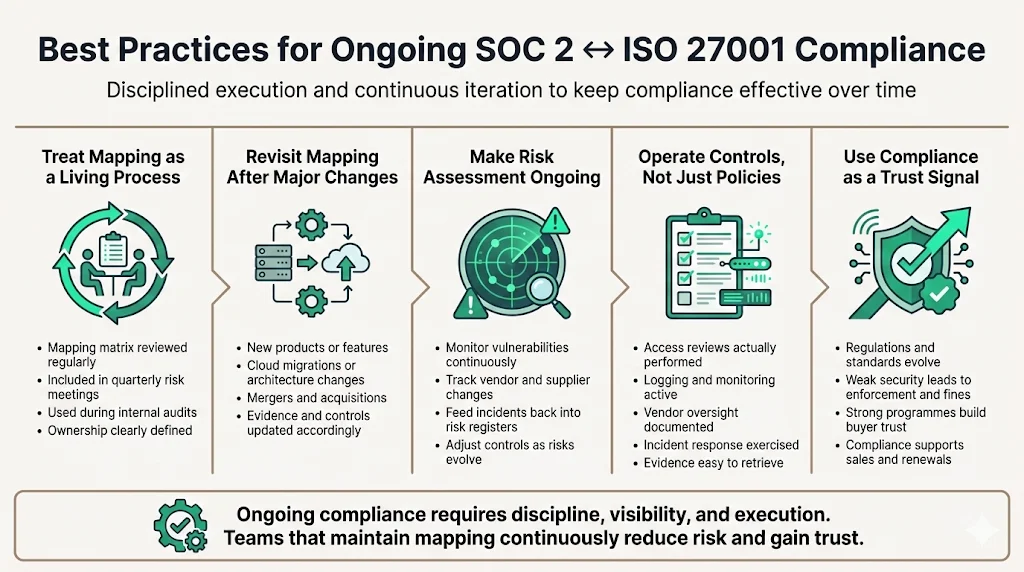
-
Embed mapping into your governance cycle. Treat the mapping matrix as a living document. Review it during quarterly risk meetings and internal audits.
-
Review mapping with every major change. New products, cloud migrations or acquisitions can introduce new risks and controls. Assess how these changes affect the mapping and update your evidence.
-
Make risk assessment continuous. Don’t treat risk assessment as an annual event. Monitor vulnerabilities, vendor changes and incidents. Update your risk register and adjust controls accordingly.
-
Use real controls — not paper promises. Ensure access reviews, logging, vendor oversight and incident response are actually performed. Evidence such as pull requests, ticket histories and vendor assessments should be easy to produce when buyers ask.
-
Stay ahead of the market. Compliance isn’t static. The 2025 ICO fines show regulators will penalise weak security practices. Organisations should treat compliance as a competitive advantage that earns trust with customers.
Conclusion
ISO 27001 Mapping To SOC 2 isn’t just a paperwork exercise; it’s a strategic way to build a single, resilient security program. ISO 27001 provides a structured management system and a globally recognised certificate. SOC 2 delivers an attestation report that U.S. buyers trust. Mapping these frameworks harnesses the overlap, reduces duplicate work, and gives teams a unified view of their controls. As someone who has guided hundreds of companies through both audits, my advice is simple: start with security and arrive at compliance. Build real controls inside your stack, collect evidence continuously, and use mapping to streamline the process. When your controls work in practice, you’ll have the artefacts to pass audits, win enterprise deals and reassure regulators.
Frequently asked questions
1) Can SOC 2 replace ISO 27001?
No. SOC 2 is an attestation, not a certification. It evaluates how controls operate against selected criteria. ISO 27001 requires an ISMS with prescribed controls and results in a certificate. While there is about an 80% overlap, each framework has unique requirements (e.g., ISO 27001’s Statement of Applicability and SOC 2’s observation window). Many customers demand both.
2) Is there a standard mapping resource for ISO 27001 and SOC 2?
Yes. The AICPA publishes a mapping spreadsheet that compares ISO 27001 controls to SOC 2 criteria. Vendors like Secureframe and Vanta also provide mapping guides. However, these are starting points. You still need to customize the mapping to your specific scope and risk environment.
3) How much control overlap actually exists between ISO 27001 and SOC 2?
AICPA’s mapping suggests roughly an 80% overlap. A‑LIGN’s benchmark report found that about 43% of SOC 2 evidence can also satisfy ISO 27001 requirements. The remainder requires additional documentation or evidence, so mapping reduces but does not eliminate work.
4) Do you have to meet all ISO 27001 and SOC 2 requirements to map them?
You must meet the requirements of whichever frameworks you pursue. Mapping doesn’t waive requirements; it shows where controls satisfy both. For example, if your SOC 2 scope includes the privacy criterion, you must implement privacy controls even though ISO 27001’s Annex A has no direct equivalent. Similarly, ISO 27001 requires formal risk treatment and internal audits, which SOC 2 doesn’t require explicitly.
5) How often should you update your control mapping?
Update the mapping at least annually or when significant changes occur: new systems, acquisitions, regulatory updates, or changes to ISO 27001 or SOC 2 criteria. Because ISO 27001:2022 requires transition by October 31 2025, organisations should review their mappings in advance. Regular updates ensure that controls remain effective and evidence stays current for audits and buyer questionnaires.




